During almost every CMMC conversation, one question inevitably comes up:
“Should we build an enclave?”
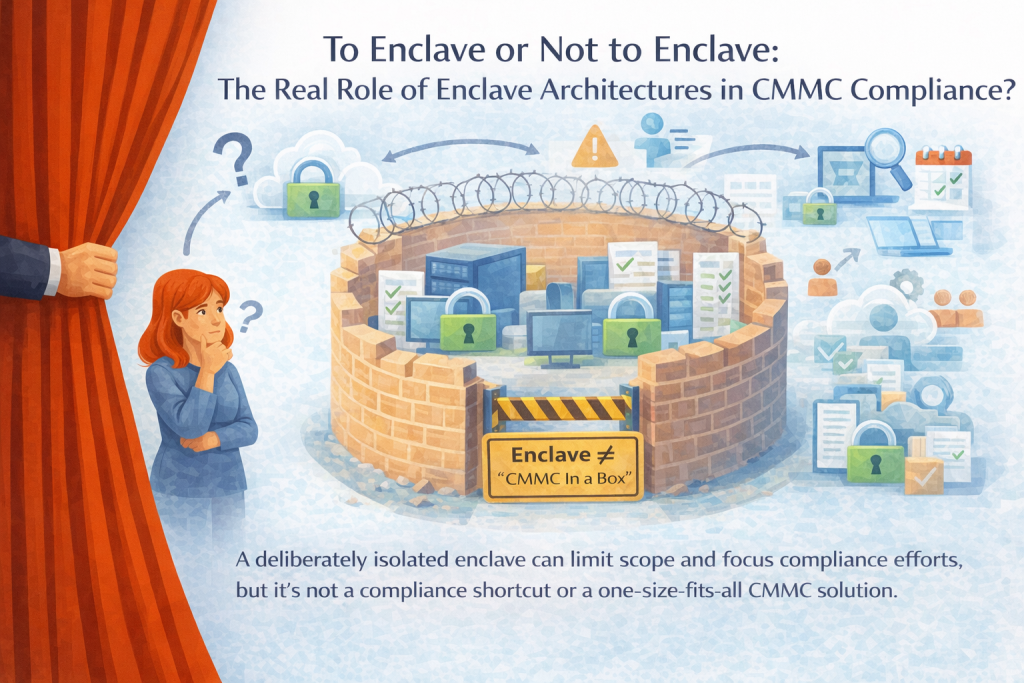
For organizations handling CUI, enclave architectures are often positioned as a shortcut…or worse, a guarantee of CMMC success. The truth is more nuanced. When designed correctly, enclaves can dramatically reduce scope, complexity, and operational drag. When misunderstood, they can create false confidence and shift risk instead of reducing it.
This post breaks down what enclaves actually do well, where they fall short, and why an enclave is not “CMMC In a Box.”
What an Enclave Really Is
At its core, a CMMC enclave is a deliberately isolated environment where all systems that store, process, or transmit CUI live. The goal is simple: limit scope.
Instead of forcing the entire organization to meet CMMC Level 2 requirements, only the enclave, the people, and processes that touch it fall into scope.
When properly implemented, this results in clearly defined boundaries, enhanced enforcement of controls, a reduced audit surface area, and fewer assumptions required during assessments.
But isolation alone does not equal compliance. An enclave is an architectural decision, not a compliance outcome.
The Real Benefits of Enclave Architecture
1. Reduced Scope, By Design
One of the biggest advantages of an enclave is scope containment.
When CUI is purposefully restricted to a defined environment:
- Fewer users are in scope
- Fewer endpoints require hardening
- Fewer workflows must meet CMMC objectives
- Fewer controls apply across the broader organization
This reduces documentation effort, evidence volume, and assessment complexity. Assessors can clearly see where CUI lives; and just as importantly, where it does not.
Scope clarity lowers risk, but only when boundaries are enforced and provable.
2. Clearer Control Ownership
Enclaves force architectural discipline.
To ensure proper management of your enclave, you must clearly establish requirements regarding access, data flow, monitoring, and review responsibilities. Begin by identifying which individuals or roles are permitted to access the enclave, such as authorized personnel with specific roles. Next, specify approved methods for data transfer, detailing how information enters and leaves the enclave (for example, through encrypted channels with management approval). Outline the logging and monitoring protocols in place, such as continuous monitoring of access logs and system activities. Finally, designate the roles responsible for reviewing security alerts and collected evidence, ensuring these tasks are handled by appropriate security team members. By defining these requirements, you help maintain a secure and well-governed enclave environment.
That clarity directly supports assessor expectations. CMMC is evaluated at the objective level, and enclaves make it easier to answer the question assessors always ask:
“How is this control implemented, enforced, and evidenced in your environment?”
When the environment is smaller and intentional, ownership is harder to dodge and easier to defend.
3. Stronger Inheritance When Used Correctly
Enclaves often rely on FedRAMP-authorized platforms for infrastructure and baseline controls. Used properly, this can reduce duplication around:
- Physical data center security
- Infrastructure-level protections
- Environmental safeguards
This allows teams to focus on the controls they cannot inherit: governance, access decisions, user behavior, logging review, incident response, and proof of execution.
Inheritance reduces burden, not accountability.
4. Operational Focus Where It Actually Matters
Rather than dispersing compliance controls throughout the entire organization, enclaves allow businesses to concentrate their compliance efforts precisely where the risk exists. This targeted approach streamlines operations by reducing the number of exceptions that need to be managed, minimizing friction for employees who are not involved with controlled unclassified information (CUI), ensuring more consistent enforcement of policies, and making evidence collection much cleaner and more straightforward.
Compliance becomes something you operate rather than something everyone trips over.
Why Enclaves Don’t Work for Everyone
Enclaves are powerful, but they are not universal.
1. Business Processes May Not Fit Clean Boundaries
If workflows involving controlled unclassified information (CUI) are deeply intertwined with the daily activities of various teams, attempting to isolate them within an enclave can disrupt collaboration, lead to redundant tasks, heighten the risk of unauthorized IT solutions, and potentially cause sensitive data to escape the enclave. In such scenarios, implementing an enclave may actually increase operational risks rather than mitigate them.
2. Cultural Readiness Matters
Establishing an enclave demands a high level of discipline from the organization. Success requires a commitment to enforcing strict access controls and refusing to make exceptions simply for the sake of convenience. Organizations must be prepared to adapt their workflows as necessary, and it is essential to provide explicit training to staff so everyone clearly understands the operational boundaries. Without these deliberate efforts, the effectiveness of the enclave is compromised.
Without buy-in, enclaves quickly degrade into “logical diagrams” instead of real protections.
3. Enclaves Add Design and Management Complexity
Isolation does not reduce the workload; instead, it centralizes it within the enclave. When enclaves are poorly designed, they can create rigid workflows, depend excessively on manual controls, conceal gaps in accountability, and ultimately fail when assessed by external reviewers. To avoid these pitfalls, the enclave’s architecture must be deliberate, thoroughly documented, and easy to maintain.
Enclave ≠ “CMMC In a Box”
One of the most dangerous myths we see is the idea that an enclave automatically makes you compliant.
It does not.
Assessors do not certify architectures. They validate execution.
If a vendor promises “compliance out of the box,” what they are really offering is tooling—not ownership.
What Organizations Still Own in an Enclave
Even with a well-designed enclave, organizations still carry essential responsibilities. They must manage user access approvals and removals, make crucial configuration decisions, enforce policies, generate and retain evidence, ensure the effectiveness of controls, and accept or mitigate risks. While an enclave can help support compliance efforts, it does not replace the need for organizations to actively own and execute these core functions.
The Real Question: Is an Enclave the Right Tool?
The enclave decision should never be framed as: “Do we want to reduce effort?”
It should be: “Does this architecture support how our business actually operates while making compliance defensible?”
When enclaves are designed to match real workflows, backed by clear responsibility mapping and disciplined execution, they can make the CMMC journey more predictable and more sustainable.
When used as a shortcut, they do the opposite.
Final Takeaway
An enclave is not a compliance strategy.
It is a boundary.
When boundaries are real, enforced, and owned, compliance becomes clearer.
When boundaries exist only on diagrams, risk multiplies.
CMMC is not about isolation.
It is about being able to clearly explain objectively, and confidently, how you protect CUI.
An enclave can help tell that story.
It can never tell the story for you.
Stay tuned for our next installment of Compliance Workshop Wednesday: How a Mock Assessment Helps Readiness. We’ll dive into the practical benefits of conducting a mock CMMC assessment, showing how it can reveal gaps, sharpen your team’s focus, and boost your confidence ahead of formal evaluations. Don’t miss this opportunity to learn strategies that make compliance preparation less daunting and more effective!
Questions about CMMC certification? Contact Hill Tech Solutions.